A new Golang-based information stealer malware dubbed Titan Stealer is being advertised by threat actors through their Telegram channel.
"The stealer is capable of stealing a variety of information from infected Windows machines, including credential data from browsers and crypto wallets, FTP client details, screenshots, system information, and grabbed files," Uptycs security researchers
http://dlvr.it/Shj9Sw
Tuesday, January 31, 2023
Realtek Vulnerability Under Attack: Over 134 Million Attempts to Hack IoT Devices
Researchers are warning about a spike in exploitation attempts weaponizing a now-patched critical remote code execution flaw in Realtek Jungle SDK since the start of August 2022.
According to Palo Alto Networks Unit 42, the ongoing campaign is said to have recorded 134 million exploit attempts as of December 2022, with 97% of the attacks occurring in the past four months.
Close to 50% of the
http://dlvr.it/Shj9FV
http://dlvr.it/Shj9FV
Monday, January 30, 2023
Black swans events are shaping the cybersecurity present and future - VentureBeat
Black swans events are shaping the cybersecurity present and future VentureBeat
http://dlvr.it/ShfHB2
http://dlvr.it/ShfHB2
Sunday, January 29, 2023
ISC Releases Security Patches for New BIND DNS Software Vulnerabilities
The Internet Systems Consortium (ISC) has released patches to address multiple security vulnerabilities in the Berkeley Internet Name Domain (BIND) 9 Domain Name System (DNS) software suite that could lead to a denial-of-service (DoS) condition.
"A remote attacker could exploit these vulnerabilities to potentially cause denial-of-service conditions and system failures," the U.S. Cybersecurity
http://dlvr.it/ShcBr0
http://dlvr.it/ShcBr0
Saturday, January 28, 2023
British Cyber Agency Warns of Russian and Iranian Hackers Targeting Key Industries
The U.K. National Cyber Security Centre (NCSC) on Thursday warned of spear-phishing attacks mounted by Russian and Iranian state-sponsored actors for information-gathering operations.
"The attacks are not aimed at the general public but targets in specified sectors, including academia, defense, government organizations, NGOs, think tanks, as well as politicians, journalists and activists," the
http://dlvr.it/ShZBKM
http://dlvr.it/ShZBKM
Friday, January 27, 2023
Researchers Uncover Connection b/w Moses Staff and Emerging Abraham's Ax Hacktivists Group
New research has linked the operations of a politically motivated hacktivist group known as Moses Staff to another nascent threat actor named Abraham's Ax that emerged in November 2022.
This is based on "several commonalities across the iconography, videography, and leak sites used by the groups, suggesting they are likely operated by the same entity," Secureworks Counter Threat Unit (CTU) said
http://dlvr.it/ShWT3T
http://dlvr.it/ShWT3T
Is Once-Yearly Pen Testing Enough for Your Organization?
Any organization that handles sensitive data must be diligent in its security efforts, which include regular pen testing. Even a small data breach can result in significant damage to an organization's reputation and bottom line.
There are two main reasons why regular pen testing is necessary for secure web application development:
Security: Web applications are constantly evolving, and new
http://dlvr.it/ShWSpd
http://dlvr.it/ShWSpd
Thursday, January 26, 2023
The Definitive Browser Security Checklist
Security stakeholders have come to realize that the prominent role the browser has in the modern corporate environment requires a re-evaluation of how it is managed and protected. While not long-ago web-borne risks were still addressed by a patchwork of endpoint, network, and cloud solutions, it is now clear that the partial protection these solutions provided is no longer sufficient. Therefore,
http://dlvr.it/ShSc1H
http://dlvr.it/ShSc1H
North Korean Hackers Turn to Credential Harvesting in Latest Wave of Cyberattacks
A North Korean nation-state group notorious for crypto heists has been attributed to a new wave of malicious email attacks as part of a "sprawling" credential harvesting activity targeting a number of industry verticals, marking a significant shift in its strategy.
The state-aligned threat actor is being tracked by Proofpoint under the name TA444, and by the larger cybersecurity community as
http://dlvr.it/ShSblM
http://dlvr.it/ShSblM
Wednesday, January 25, 2023
Apple Issues Updates for Older Devices to Fix Actively Exploited Vulnerability
Apple has backported fixes for a recently disclosed critical security flaw affecting older devices, citing evidence of active exploitation.
The issue, tracked as CVE-2022-42856, is a type confusion vulnerability in the WebKit browser engine that could result in arbitrary code execution when processing maliciously crafted web content.
While it was originally addressed by the company on November
http://dlvr.it/ShPjJk
http://dlvr.it/ShPjJk
Tuesday, January 24, 2023
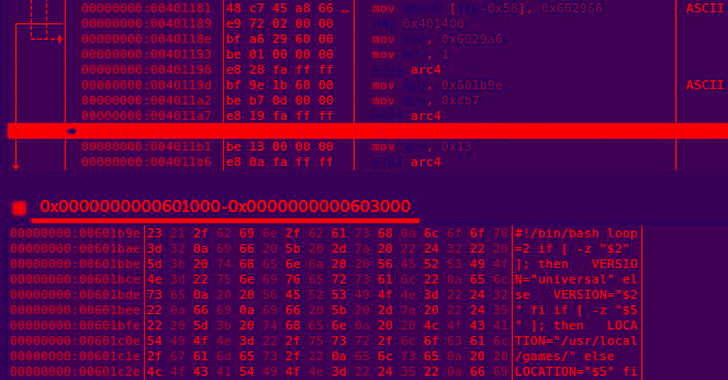
Threat Actors Turn to Sliver as Open Source Alternative to Popular C2 Frameworks
The legitimate command-and-control (C2) framework known as Sliver is gaining more traction from threat actors as it emerges as an open source alternative to Cobalt Strike and Metasploit.
The findings come from Cybereason, which detailed its inner workings in an exhaustive analysis last week.
Sliver, developed by cybersecurity company BishopFox, is a Golang-based cross-platform post-exploitation
http://dlvr.it/ShLnLc
http://dlvr.it/ShLnLc
Monday, January 23, 2023
Massive Ad Fraud Scheme Targeted Over 11 Million Devices with 1,700 Spoofed Apps
Researchers have shut down an "expansive" ad fraud scheme that spoofed more than 1,700 applications from 120 publishers and impacted roughly 11 million devices.
"VASTFLUX was a malvertising attack that injected malicious JavaScript code into digital ad creatives, allowing the fraudsters to stack numerous invisible video ad players behind one another and register ad views," fraud prevention firm
http://dlvr.it/ShHz6D
http://dlvr.it/ShHz6D
Sunday, January 22, 2023
Sen. Mitch McConnell visits UofL to announce $20 million in federal ... - uoflnews.com
Sen. Mitch McConnell visits UofL to announce $20 million in federal ... uoflnews.com
http://dlvr.it/ShFxd8
http://dlvr.it/ShFxd8
Saturday, January 21, 2023
WhatsApp Hit with €5.5 Million Fine for Violating Data Protection Laws
The Irish Data Protection Commission (DPC) on Thursday imposed fresh fines of €5.5 million against Meta's WhatsApp for violating data protection laws when processing users' personal information.
At the heart of the ruling is an update to the messaging platform's Terms of Service that was imposed in the days leading to the enforcement of the General Data Protection Regulation (GDPR) in May 2018,
http://dlvr.it/ShCydb
http://dlvr.it/ShCydb
Friday, January 20, 2023
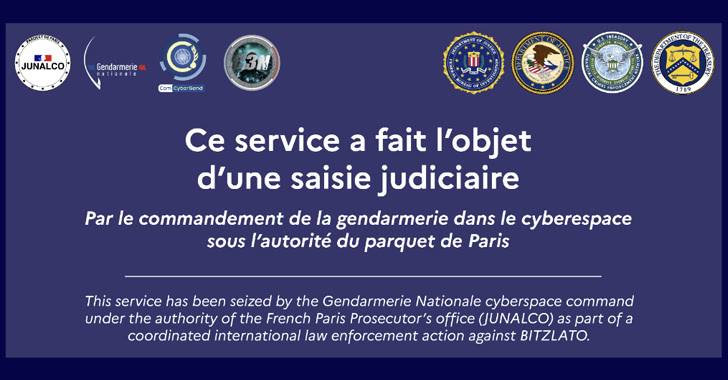
Bitzlato Crypto Exchange Founder Arrested for Aiding Cybercriminals
The U.S. Department of Justice (DoJ) on Wednesday announced the arrest of Anatoly Legkodymov (aka Gandalf and Tolik), the cofounder of Hong Kong-registered cryptocurrency exchange Bitzlato, for allegedly processing $700 million in illicit funds.
The 40-year-old Russian national, who was arrested in Miami, was charged in a U.S. federal court with "conducting a money transmitting business that
http://dlvr.it/Sh9B9Q
http://dlvr.it/Sh9B9Q
Thursday, January 19, 2023
Git Users Urged to Update Software to Prevent Remote Code Execution Attacks
The maintainers of the Git source code version control system have released updates to remediate two critical vulnerabilities that could be exploited by a malicious actor to achieve remote code execution.
The flaws, tracked as CVE-2022-23521 and CVE-2022-41903, impacts the following versions of Git: v2.30.6, v2.31.5, v2.32.4, v2.33.5, v2.34.5, v2.35.5, v2.36.3, v2.37.4, v2.38.2, and v2.39.0.
http://dlvr.it/Sh6Dl2
http://dlvr.it/Sh6Dl2
Wednesday, January 18, 2023
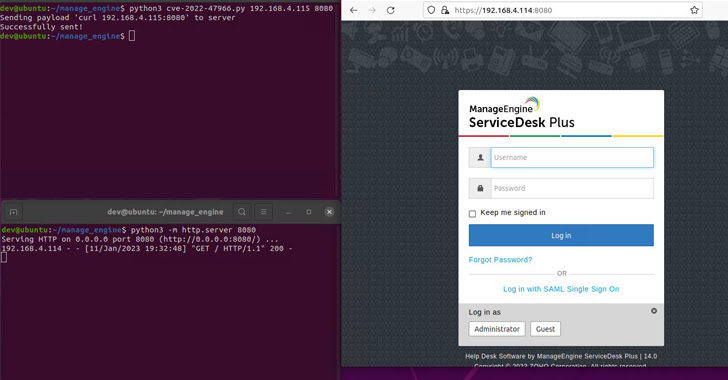
Zoho ManageEngine PoC Exploit to be Released Soon - Patch Before It's Too Late!
Users of Zoho ManageEngine are being urged to patch their instances against a critical security vulnerability ahead of the release of a proof-of-concept (PoC) exploit code.
The issue in question is CVE-2022-47966, an unauthenticated remote code execution vulnerability affecting several products due to the use of an outdated third-party dependency, Apache Santuario.
"This vulnerability allows an
http://dlvr.it/Sh3DzQ
http://dlvr.it/Sh3DzQ
Tuesday, January 17, 2023
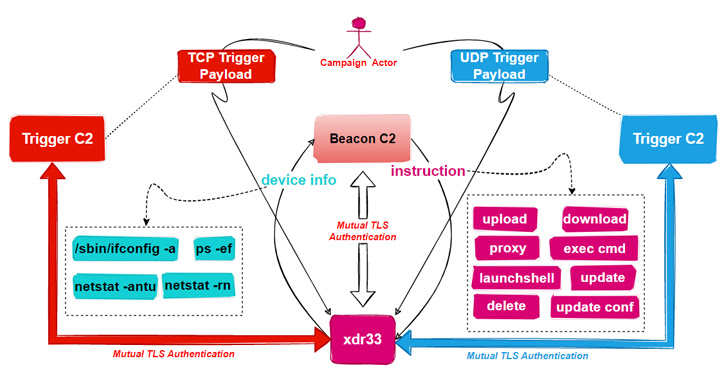
New Backdoor Created Using Leaked CIA's Hive Malware Discovered in the Wild
Unidentified threat actors have deployed a new backdoor that borrows its features from the U.S. Central Intelligence Agency (CIA)'s Hive multi-platform malware suite, the source code of which was released by WikiLeaks in November 2017.
"This is the first time we caught a variant of the CIA Hive attack kit in the wild, and we named it xdr33 based on its embedded Bot-side certificate CN=xdr33,"
http://dlvr.it/Sh0F0p
http://dlvr.it/Sh0F0p
Monday, January 16, 2023
Sunday, January 15, 2023
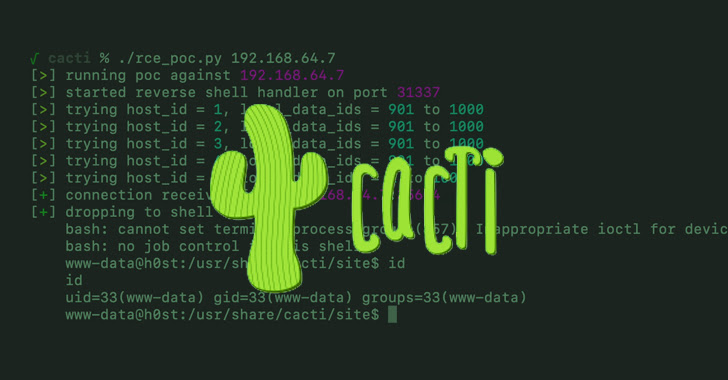
Cacti Servers Under Attack as Majority Fail to Patch Critical Vulnerability
A majority of internet-exposed Cacti servers have not been patched against a recently patched critical security vulnerability that has come under active exploitation in the wild.
That's according to attack surface management platform Censys, which found only 26 out of a total of 6,427 servers to be running a patched version of Cacti (1.2.23 and 1.3.0).
The issue in question relates to
http://dlvr.it/SgvNxm
http://dlvr.it/SgvNxm
Saturday, January 14, 2023
FortiOS Flaw Exploited as Zero-Day in Attacks on Government and Organizations
A zero-day vulnerability in FortiOS SSL-VPN that Fortinet addressed last month was exploited by unknown actors in attacks targeting the government and other large organizations.
"The complexity of the exploit suggests an advanced actor and that it is highly targeted at governmental or government-related targets," Fortinet researchers said in a post-mortem analysis published this week.
The
http://dlvr.it/SgsPCd
http://dlvr.it/SgsPCd
Friday, January 13, 2023
Twitter Denies Hacking Claims, Assures Leaked User Data Not from its System
Twitter on Wednesday said that its investigation found "no evidence" that users' data sold online was obtained by exploiting any security vulnerabilities in its systems.
"Based on information and intel analyzed to investigate the issue, there is no evidence that the data being sold online was obtained by exploiting a vulnerability of Twitter systems," the company said in a statement. "The data
http://dlvr.it/SgphFq
http://dlvr.it/SgphFq
Thursday, January 12, 2023
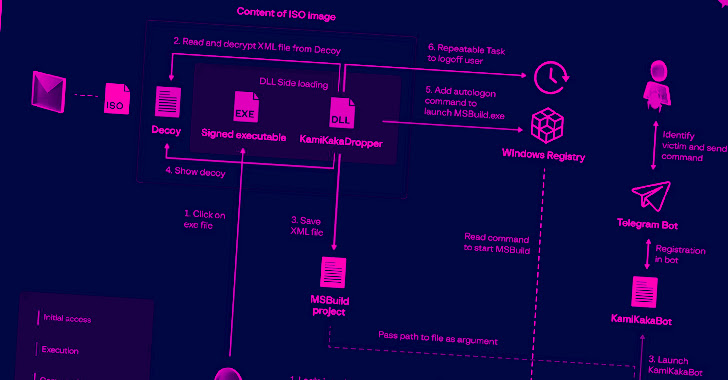
Dark Pink APT Group Targets Governments and Military in APAC Region
Government and military organizations in the Asia-Pacific region are being targeted by a previously unknown advanced persistent threat (APT) actor, per the latest research conducted by Albert Priego of Group-IB
Singapore-headquartered Group-IB, in a report shared with The Hacker News, said it's tracking the ongoing campaign under the name Dark Pink and attributed seven successful attacks to the
http://dlvr.it/Sglmyp
http://dlvr.it/Sglmyp
Wednesday, January 11, 2023
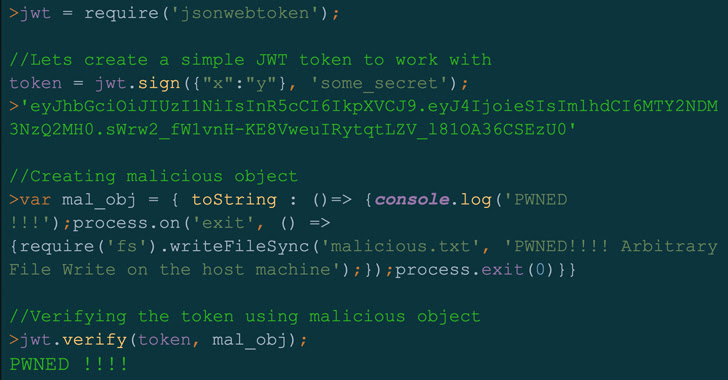
Severe Security Flaw Found in "jsonwebtoken" Library Used by 22,000+ Projects
A high-severity security flaw has been disclosed in the open source jsonwebtoken (JWT) library that, if successfully exploited, could lead to remote code execution on a target server.
"By exploiting this vulnerability, attackers could achieve remote code execution (RCE) on a server verifying a maliciously crafted JSON web token (JWT) request," Palo Alto Networks Unit 42 researcher Artur Oleyarsh
http://dlvr.it/Sghv82
http://dlvr.it/Sghv82
Tuesday, January 10, 2023
Top SaaS Cybersecurity Threats in 2023: Are You Ready?
Cybercriminals will be as busy as ever this year. Stay safe and protect your systems and data by focusing on these 4 key areas to secure your environment and ensure success in 2023, and make sure your business is only in the headlines when you WANT it to be. 1 — Web application weaknesses
Web applications are at the core of what SaaS companies do and how they operate, and they can store some of
http://dlvr.it/SgdzFD
http://dlvr.it/SgdzFD
Monday, January 9, 2023
Hackers Can Abuse Visual Studio Marketplace to Target Developers with Malicious Extensions
A new attack vector targeting the Visual Studio Code extensions marketplace could be leveraged to upload rogue extensions masquerading as their legitimate counterparts with the goal of mounting supply chain attacks.
The technique "could act as an entry point for an attack on many organizations," Aqua security researcher Ilay Goldman said in a report published last week.
VS Code extensions,
http://dlvr.it/Sgb8F5
http://dlvr.it/Sgb8F5
Sunday, January 8, 2023
Russian Turla Hackers Hijack Decade-Old Malware Infrastructure to Deploy New Backdoors
The Russian cyberespionage group known as Turla has been observed piggybacking on attack infrastructure used by a decade-old malware to deliver its own reconnaissance and backdoor tools to targets in Ukraine.
Google-owned Mandiant, which is tracking the operation under the uncategorized cluster moniker UNC4210, said the hijacked servers correspond to a variant of a commodity malware called
http://dlvr.it/SgY6xR
http://dlvr.it/SgY6xR
Saturday, January 7, 2023
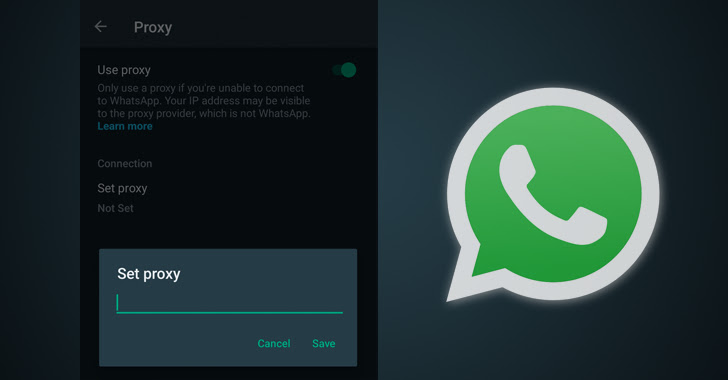
WhatsApp Introduces Proxy Support to Help Users Bypass Internet Censorship
Popular instant messaging service WhatsApp has launched support for proxy servers in the latest version of its Android and iOS apps, letting users circumvent government-imposed censorship and internet shutdowns.
"Choosing a proxy enables you to connect to WhatsApp through servers set up by volunteers and organizations around the world dedicated to helping people communicate freely," the
http://dlvr.it/SgW9cd
http://dlvr.it/SgW9cd
Friday, January 6, 2023
Fortinet and Zoho Urge Customers to Patch Enterprise Software Vulnerabilities
Fortinet has warned of a high-severity flaw affecting multiple versions of FortiADC application delivery controller that could lead to the execution of arbitrary code.
"An improper neutralization of special elements used in an OS command vulnerability in FortiADC may allow an authenticated attacker with access to the web GUI to execute unauthorized code or commands via specifically crafted HTTP
http://dlvr.it/SgScXv
http://dlvr.it/SgScXv
Thursday, January 5, 2023
New shc-based Linux Malware Targeting Systems with Cryptocurrency Miner
A new Linux malware developed using the shell script compiler (shc) has been observed deploying a cryptocurrency miner on compromised systems.
"It is presumed that after successful authentication through a dictionary attack on inadequately managed Linux SSH servers, various malware were installed on the target system," AhnLab Security Emergency Response Center (ASEC) said in a report published
http://dlvr.it/SgPqKp
http://dlvr.it/SgPqKp
Wednesday, January 4, 2023
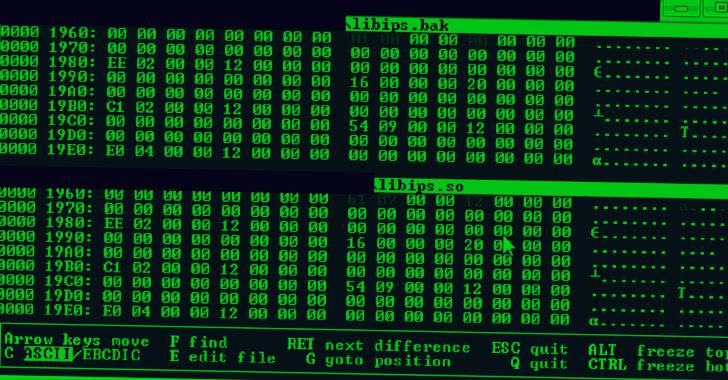
Raspberry Robin Worm Evolves to Attack Financial and Insurance Sectors in Europe
Financial and insurance sectors in Europe have been targeted by the Raspberry Robin worm, as the malware continues to evolve its post-exploitation capabilities while remaining under the radar.
"What is unique about the malware is that it is heavily obfuscated and highly complex to statically disassemble," Security Joes said in a new report published Monday.
The intrusions, observed against
http://dlvr.it/SgLwFF
http://dlvr.it/SgLwFF
Tuesday, January 3, 2023
Google to Pay $29.5 Million to Settle Lawsuits Over User Location Tracking
Google has agreed to pay a total of $29.5 million to settle two different lawsuits brought by Indiana and Washington, D.C., over its "deceptive" location tracking practices.
The search and advertising giant is required to pay $9.5 million to D.C. and $20 million to Indiana after the states sued the company for charges that the company tracked users' locations without their express consent.
The
http://dlvr.it/SgJ24B
http://dlvr.it/SgJ24B
Monday, January 2, 2023
Cybersecurity Experts Uncover Inner Workings of Destructive Azov Ransomware - The Hacker News
Cybersecurity Experts Uncover Inner Workings of Destructive Azov Ransomware The Hacker News
http://dlvr.it/SgFYyk
http://dlvr.it/SgFYyk
Sunday, January 1, 2023
Subscribe to:
Posts (Atom)
Cybersecurity needs AI as much as AI needs cybersecurity - Techzine Europe
Cybersecurity needs AI as much as AI needs cybersecurity Techzine Europe http://dlvr.it/TDY1dr
-
This statistic presents a ranking of the countries with the highest commitment to cyber security based on the Global Cybersecurity Index (GC...
-
Supply chain cyberattacks threaten healthcare. Here’s how the industry can work together to limit disruption. Healthcare Dive http://dlvr...
-
Cybersecurity needs AI as much as AI needs cybersecurity Techzine Europe http://dlvr.it/TDY1dr