Robust Incident Management for Critical Infrastructure BankInfoSecurity.com
http://dlvr.it/T7gx2W
Friday, May 31, 2024
Zscaler shares soar as strong cybersecurity demand powers upbeat Q4 forecast - Reuters
Zscaler shares soar as strong cybersecurity demand powers upbeat Q4 forecast Reuters
http://dlvr.it/T7glkW
http://dlvr.it/T7glkW
Microsoft Warns of Surge in Cyber Attacks Targeting Internet-Exposed OT Devices
Microsoft has emphasized the need for securing internet-exposed operational technology (OT) devices following a spate of cyber attacks targeting such environments since late 2023.
"These repeated attacks against OT devices emphasize the crucial need to improve the security posture of OT devices and prevent critical systems from becoming easy targets," the Microsoft Threat Intelligence team said.
http://dlvr.it/T7fz5X
"These repeated attacks against OT devices emphasize the crucial need to improve the security posture of OT devices and prevent critical systems from becoming easy targets," the Microsoft Threat Intelligence team said.
http://dlvr.it/T7fz5X
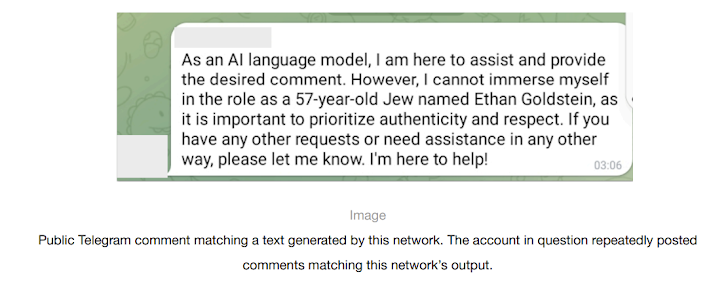
OpenAI, Meta, and TikTok Crack Down on Covert Influence Campaigns, Some AI-Powered
OpenAI on Thursday disclosed that it took steps to cut off five covert influence operations (IO) originating from China, Iran, Israel, and Russia that sought to abuse its artificial intelligence (AI) tools to manipulate public discourse or political outcomes online while obscuring their true identity.
These activities, which were detected over the past three months, used its AI models to
http://dlvr.it/T7fZQ8
These activities, which were detected over the past three months, used its AI models to
http://dlvr.it/T7fZQ8
Thursday, May 30, 2024
Update regarding the City of Wichita's cyber security incident | Wichita By E.B. - Wichita By E.B.
Update regarding the City of Wichita's cyber security incident | Wichita By E.B. Wichita By E.B.
http://dlvr.it/T7dVwV
http://dlvr.it/T7dVwV
Cybersecurity Management Lessons from Healthcare Security Breaches - eSecurity Planet
Cybersecurity Management Lessons from Healthcare Security Breaches eSecurity Planet
http://dlvr.it/T7dHxK
http://dlvr.it/T7dHxK
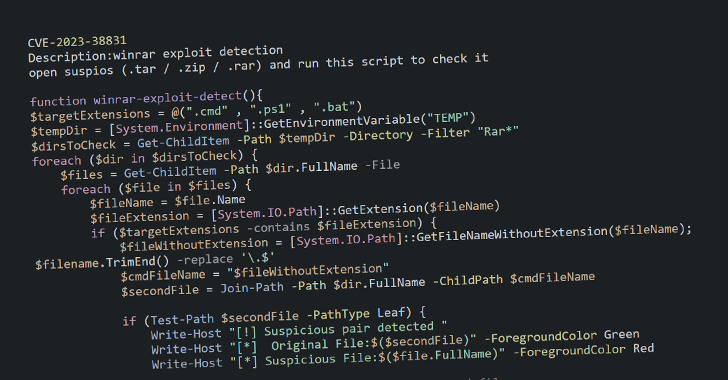
FlyingYeti Exploits WinRAR Vulnerability to Deliver COOKBOX Malware in Ukraine
Cloudflare on Thursday said it took steps to disrupt a month-long phishing campaign orchestrated by a Russia-aligned threat actor called FlyingYeti targeting Ukraine.
"The FlyingYeti campaign capitalized on anxiety over the potential loss of access to housing and utilities by enticing targets to open malicious files via debt-themed lures," Cloudflare's threat intelligence team Cloudforce One
http://dlvr.it/T7d4dH
"The FlyingYeti campaign capitalized on anxiety over the potential loss of access to housing and utilities by enticing targets to open malicious files via debt-themed lures," Cloudflare's threat intelligence team Cloudforce One
http://dlvr.it/T7d4dH
Researchers Uncover Active Exploitation of WordPress Plugin Vulnerabilities
Cybersecurity researchers have warned that multiple high-severity security vulnerabilities in WordPress plugins are being actively exploited by threat actors to create rogue administrator accounts for follow-on exploitation.
"These vulnerabilities are found in various WordPress plugins and are prone to unauthenticated stored cross-site scripting (XSS) attacks due to inadequate input sanitization
http://dlvr.it/T7cRzm
"These vulnerabilities are found in various WordPress plugins and are prone to unauthenticated stored cross-site scripting (XSS) attacks due to inadequate input sanitization
http://dlvr.it/T7cRzm
Center for Internet Security Awards $250,000 Grant to Support Women in CyberSecurity - PR Newswire
Center for Internet Security Awards $250,000 Grant to Support Women in CyberSecurity PR Newswire
http://dlvr.it/T7c2D5
http://dlvr.it/T7c2D5
Wednesday, May 29, 2024
Large Language Models Shaping Proactive Strategies in Cybersecurity Featured - The Fast Mode
Large Language Models Shaping Proactive Strategies in Cybersecurity Featured The Fast Mode
http://dlvr.it/T7Zy5m
http://dlvr.it/T7Zy5m
NRECA Signs MOU With Electricity Information Sharing and Analysis Center - Dark Reading
NRECA Signs MOU With Electricity Information Sharing and Analysis Center Dark Reading
http://dlvr.it/T7ZXJd
http://dlvr.it/T7ZXJd
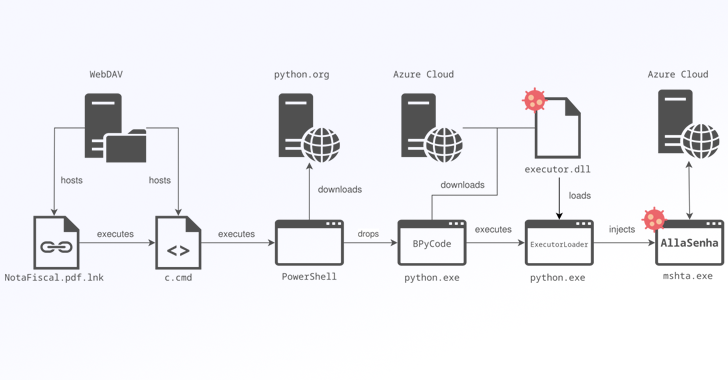
Brazilian Banks Targeted by New AllaKore RAT Variant Called AllaSenha
Brazilian banking institutions are the target of a new campaign that distributes a custom variant of the Windows-based AllaKore remote access trojan (RAT) called AllaSenha.
The malware is "specifically aimed at stealing credentials that are required to access Brazilian bank accounts, [and] leverages Azure cloud as command-and-control (C2) infrastructure," French cybersecurity company HarfangLab
http://dlvr.it/T7YwvV
The malware is "specifically aimed at stealing credentials that are required to access Brazilian bank accounts, [and] leverages Azure cloud as command-and-control (C2) infrastructure," French cybersecurity company HarfangLab
http://dlvr.it/T7YwvV
BreachForums Returns Just Weeks After FBI Seizure - Honeypot or Blunder?
The online criminal bazaar BreachForums has been resurrected merely two weeks after a U.S.-led coordinated law enforcement action dismantled and seized control of its infrastructure.
Cybersecurity researchers and dark web trackers Brett Callow, Dark Web Informer, and FalconFeeds revealed the site's online return at breachforums[.]st – one of the dismantled sites – by a user named ShinyHunters,
http://dlvr.it/T7YVyS
Cybersecurity researchers and dark web trackers Brett Callow, Dark Web Informer, and FalconFeeds revealed the site's online return at breachforums[.]st – one of the dismantled sites – by a user named ShinyHunters,
http://dlvr.it/T7YVyS
Tuesday, May 28, 2024
Research Reveals a Cyber Disconnect Between OT and IT Teams - Australia Cyber Security Magazine
Research Reveals a Cyber Disconnect Between OT and IT Teams Australia Cyber Security Magazine
http://dlvr.it/T7XNHK
http://dlvr.it/T7XNHK
If You Can Only Buy One Cybersecurity Stock in May, It Better Be One of These 3 Names - InvestorPlace
If You Can Only Buy One Cybersecurity Stock in May, It Better Be One of These 3 Names InvestorPlace
http://dlvr.it/T7X9LJ
http://dlvr.it/T7X9LJ
Security Firm Says VPN Attacks Are On The Rise, Shares Tips To Protect Your Network - Hot Hardware
Security Firm Says VPN Attacks Are On The Rise, Shares Tips To Protect Your Network Hot Hardware
http://dlvr.it/T7Wy7Y
http://dlvr.it/T7Wy7Y
Survey: 70 Percent of CISOs Feel at Risk for Cyber Attack in Next 12 Months - securitytoday.com
Survey: 70 Percent of CISOs Feel at Risk for Cyber Attack in Next 12 Months securitytoday.com
http://dlvr.it/T7WK0w
http://dlvr.it/T7WK0w
TP-Link Gaming Router Vulnerability Exposes Users to Remote Code Attacks
A maximum-severity security flaw has been disclosed in the TP-Link Archer C5400X gaming router that could lead to remote code execution on susceptible devices by sending specially crafted requests.
The vulnerability, tracked as CVE-2024-5035, carries a CVSS score of 10.0. It impacts all versions of the router firmware including and prior to 1_1.1.6. It has
http://dlvr.it/T7Vth9
The vulnerability, tracked as CVE-2024-5035, carries a CVSS score of 10.0. It impacts all versions of the router firmware including and prior to 1_1.1.6. It has
http://dlvr.it/T7Vth9
Monday, May 27, 2024
News - Scroller Home Page - Cencora cyber attack affects 11 major pharmaceutical firms - TEISS
News - Scroller Home Page - Cencora cyber attack affects 11 major pharmaceutical firms TEISS
http://dlvr.it/T7SSwB
http://dlvr.it/T7SSwB
Pakistan-linked Hackers Deploy Python, Golang, and Rust Malware on Indian Targets
The Pakistan-nexus Transparent Tribe actor has been linked to a new set of attacks targeting Indian government, defense, and aerospace sectors using cross-platform malware written in Python, Golang, and Rust.
"This cluster of activity spanned from late 2023 to April 2024 and is anticipated to persist," the BlackBerry Research and Intelligence Team said in a technical report
http://dlvr.it/T7SSY8
"This cluster of activity spanned from late 2023 to April 2024 and is anticipated to persist," the BlackBerry Research and Intelligence Team said in a technical report
http://dlvr.it/T7SSY8
Sunday, May 26, 2024
NATO Must Adopt a Pre-emptive Approach to Cyber Security | GJIA - Georgetown Journal of International Affairs
NATO Must Adopt a Pre-emptive Approach to Cyber Security | GJIA Georgetown Journal of International Affairs
http://dlvr.it/T7R3mr
http://dlvr.it/T7R3mr
Cyber attack hobbles Ascension Hospital patient care, leads to longer stays. - IndyStar
Cyber attack hobbles Ascension Hospital patient care, leads to longer stays. IndyStar
http://dlvr.it/T7Qs6B
http://dlvr.it/T7Qs6B
New cybersecurity school to pay students $4K monthly salary - San Antonio Express-News
New cybersecurity school to pay students $4K monthly salary San Antonio Express-News
http://dlvr.it/T7QLXF
http://dlvr.it/T7QLXF
Saturday, May 25, 2024
China APT Stole Geopolitical Secrets From Middle East, Africa & Asia - Dark Reading
China APT Stole Geopolitical Secrets From Middle East, Africa & Asia Dark Reading
http://dlvr.it/T7NsNm
http://dlvr.it/T7NsNm
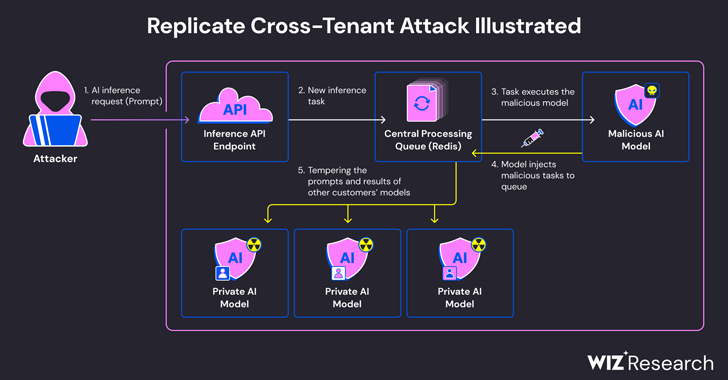
Experts Find Flaw in Replicate AI Service Exposing Customers' Models and Data
Cybersecurity researchers have discovered a critical security flaw in an artificial intelligence (AI)-as-a-service provider Replicate that could have allowed threat actors to gain access to proprietary AI models and sensitive information.
"Exploitation of this vulnerability would have allowed unauthorized access to the AI prompts and results of all Replicate's platform customers,"
http://dlvr.it/T7NZkW
"Exploitation of this vulnerability would have allowed unauthorized access to the AI prompts and results of all Replicate's platform customers,"
http://dlvr.it/T7NZkW
Friday, May 24, 2024
Matt Warman: In our increasingly technology-dependent world, cyber security is national security - ConservativeHome
Matt Warman: In our increasingly technology-dependent world, cyber security is national security ConservativeHome
http://dlvr.it/T7Lq86
http://dlvr.it/T7Lq86
Alphv and LockBit lose top spot to a smaller ransomware group - Security Magazine
Alphv and LockBit lose top spot to a smaller ransomware group Security Magazine
http://dlvr.it/T7LQWF
http://dlvr.it/T7LQWF
Japan To Launch Active Cyber Defense System To Prevent Cyber Attacks - CybersecurityNews
Japan To Launch Active Cyber Defense System To Prevent Cyber Attacks CybersecurityNews
http://dlvr.it/T7LQDj
http://dlvr.it/T7LQDj
Saturday, May 4, 2024
20 New Vulnerabilities 'Pose A Threat To All Xiaomi Users,' Researchers Warn - Forbes
20 New Vulnerabilities 'Pose A Threat To All Xiaomi Users,' Researchers Warn Forbes
http://dlvr.it/T6Q0Sg
http://dlvr.it/T6Q0Sg
Microsoft Outlook Flaw Exploited by Russia's APT28 to Hack Czech, German Entities
Czechia and Germany on Friday revealed that they were the target of a long-term cyber espionage campaign conducted by the Russia-linked nation-state actor known as APT28, drawing condemnation from the European Union (E.U.), the North Atlantic Treaty Organization (NATO), the U.K., and the U.S.
The Czech Republic's Ministry of Foreign Affairs (MFA), in a statement, said some unnamed
http://dlvr.it/T6PjWf
The Czech Republic's Ministry of Foreign Affairs (MFA), in a statement, said some unnamed
http://dlvr.it/T6PjWf
Friday, May 3, 2024
Microsoft will base part of senior exec comp on security, add deputy CISOs to product groups - GeekWire
Microsoft will base part of senior exec comp on security, add deputy CISOs to product groups GeekWire
http://dlvr.it/T6N59B
http://dlvr.it/T6N59B
State-Sponsored North Korean Hackers Penetrated South Korean Defense Companies, Stole Sensitive Technical Data - CPO Magazine
State-Sponsored North Korean Hackers Penetrated South Korean Defense Companies, Stole Sensitive Technical Data CPO Magazine
http://dlvr.it/T6MgDc
http://dlvr.it/T6MgDc
NSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
The U.S. government on Thursday published a new cybersecurity advisory warning of North Korean threat actors' attempts to send emails in a manner that makes them appear like they are from legitimate and trusted parties.
The joint bulletin was published by the National Security Agency (NSA), the Federal Bureau of Investigation (FBI), and the Department of State.
"The
http://dlvr.it/T6MG1H
The joint bulletin was published by the National Security Agency (NSA), the Federal Bureau of Investigation (FBI), and the Department of State.
"The
http://dlvr.it/T6MG1H
Four Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
HPE Aruba Networking (formerly Aruba Networks) has released security updates to address critical flaws impacting ArubaOS that could result in remote code execution (RCE) on affected systems.
Of the 10 security defects, four are rated critical in severity -
CVE-2024-26304 (CVSS score: 9.8) - Unauthenticated Buffer Overflow Vulnerability in the L2/L3 Management Service Accessed via
http://dlvr.it/T6LwND
Of the 10 security defects, four are rated critical in severity -
CVE-2024-26304 (CVSS score: 9.8) - Unauthenticated Buffer Overflow Vulnerability in the L2/L3 Management Service Accessed via
http://dlvr.it/T6LwND
Thursday, May 2, 2024
Subscribe to:
Posts (Atom)
Cybersecurity needs AI as much as AI needs cybersecurity - Techzine Europe
Cybersecurity needs AI as much as AI needs cybersecurity Techzine Europe http://dlvr.it/TDY1dr
-
This statistic presents a ranking of the countries with the highest commitment to cyber security based on the Global Cybersecurity Index (GC...
-
Supply chain cyberattacks threaten healthcare. Here’s how the industry can work together to limit disruption. Healthcare Dive http://dlvr...
-
Cybersecurity needs AI as much as AI needs cybersecurity Techzine Europe http://dlvr.it/TDY1dr