Japan's space agency suffers cyber attack, points finger at Active Directory The Register
http://dlvr.it/SzXmRl
Thursday, November 30, 2023
North Texas water utility the latest suspected industrial ransomware ... - Cybersecurity Dive
North Texas water utility the latest suspected industrial ransomware ... Cybersecurity Dive
http://dlvr.it/SzXWSt
http://dlvr.it/SzXWSt
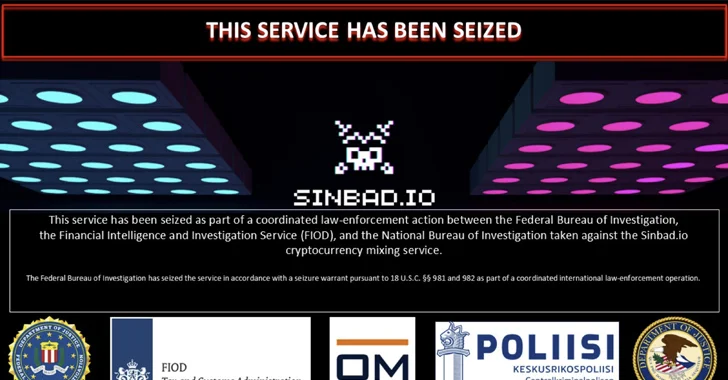
U.S. Treasury Sanctions Sinbad Cryptocurrency Mixer Used by North Korean Hackers
The U.S. Treasury Department on Wednesday imposed sanctions against Sinbad, a virtual currency mixer that has been put to use by the North Korea-linked Lazarus Group to launder ill-gotten proceeds.
"Sinbad has processed millions of dollars' worth of virtual currency from Lazarus Group heists, including the Horizon Bridge and Axie Infinity heists," the department said.
"Sinbad is also used by
http://dlvr.it/SzWmMq
"Sinbad has processed millions of dollars' worth of virtual currency from Lazarus Group heists, including the Horizon Bridge and Axie Infinity heists," the department said.
"Sinbad is also used by
http://dlvr.it/SzWmMq
Wednesday, November 29, 2023
Cyber Security Issue at North Texas Municipal Water District - EastTexasRadio.com
Cyber Security Issue at North Texas Municipal Water District EastTexasRadio.com
http://dlvr.it/SzTD0l
http://dlvr.it/SzTD0l
Tuesday, November 28, 2023
N. Korean Hackers 'Mixing' macOS Malware Tactics to Evade Detection
The North Korean threat actors behind macOS malware strains such as RustBucket and KANDYKORN have been observed "mixing and matching" different elements of the two disparate attack chains, leveraging RustBucket droppers to deliver KANDYKORN.
The findings come from cybersecurity firm SentinelOne, which also tied a third macOS-specific malware called ObjCShellz to the RustBucket campaign.
http://dlvr.it/SzQdYD
The findings come from cybersecurity firm SentinelOne, which also tied a third macOS-specific malware called ObjCShellz to the RustBucket campaign.
http://dlvr.it/SzQdYD
Monday, November 27, 2023
How to Handle Retail SaaS Security on Cyber Monday
If forecasters are right, over the course of today, consumers will spend $13.7 billion. Just about every click, sale, and engagement will be captured by a CRM platform. Inventory applications will trigger automated re-orders; communication tools will send automated email and text messages confirming sales and sharing shipping information.
SaaS applications supporting retail efforts will host
http://dlvr.it/SzNr4K
SaaS applications supporting retail efforts will host
http://dlvr.it/SzNr4K
Apple's iPhone iOS17 NameDrop feature "major red flag" for cybersecurity, expert says - CBS Philly
Apple's iPhone iOS17 NameDrop feature "major red flag" for cybersecurity, expert says CBS Philly
http://dlvr.it/SzNVX8
http://dlvr.it/SzNVX8
U.S., U.K., and Global Partners Release Secure AI System Development Guidelines
The U.K. and U.S., along with international partners from 16 other countries, have released new guidelines for the development of secure artificial intelligence (AI) systems.
"The approach prioritizes ownership of security outcomes for customers, embraces radical transparency and accountability, and establishes organizational structures where secure design is a top priority," the U.S.
http://dlvr.it/SzN5sZ
"The approach prioritizes ownership of security outcomes for customers, embraces radical transparency and accountability, and establishes organizational structures where secure design is a top priority," the U.S.
http://dlvr.it/SzN5sZ
Sunday, November 26, 2023
Hardware security keys are one way you can keep your accounts safe - The Arizona Republic
Hardware security keys are one way you can keep your accounts safe The Arizona Republic
http://dlvr.it/SzLHP3
http://dlvr.it/SzLHP3
Potential cybersecurity incident leaves hospitals without ambulances - WKRC TV Cincinnati
Potential cybersecurity incident leaves hospitals without ambulances WKRC TV Cincinnati
http://dlvr.it/SzLH8s
http://dlvr.it/SzLH8s
In Other News: National Laboratory Breach, Airplane GPS Attacks, Russia Accuses Allies of Hacking - SecurityWeek
In Other News: National Laboratory Breach, Airplane GPS Attacks, Russia Accuses Allies of Hacking SecurityWeek
http://dlvr.it/SzLGxn
http://dlvr.it/SzLGxn
Rhysida ransomware group claims crippling British Library cyber attack | Cyber Security Hub - Cyber Security Hub
Rhysida ransomware group claims crippling British Library cyber attack | Cyber Security Hub Cyber Security Hub
http://dlvr.it/SzLGlS
http://dlvr.it/SzLGlS
GCHQ investigates cyber attack on hospital to the royals after data ... - The Telegraph
GCHQ investigates cyber attack on hospital to the royals after data ... The Telegraph
http://dlvr.it/SzL0xn
http://dlvr.it/SzL0xn
Saturday, November 25, 2023
Media Release: CYBERCOM executes international coordinated ... - United States Cyber Command
Media Release: CYBERCOM executes international coordinated ... United States Cyber Command
http://dlvr.it/SzJbwn
http://dlvr.it/SzJbwn
TSA updates, renews cybersecurity requirements for pipeline ... - Transportation Security Administration
TSA updates, renews cybersecurity requirements for pipeline ... Transportation Security Administration
http://dlvr.it/SzJbbK
http://dlvr.it/SzJbbK
Cybercriminals Using Telekopye Telegram Bot to Craft Phishing Scams on a Grand Scale
More details have emerged about a malicious Telegram bot called Telekopye that's used by threat actors to pull off large-scale phishing scams.
"Telekopye can craft phishing websites, emails, SMS messages, and more," ESET security researcher Radek Jizba said in a new analysis.
The threat actors behind the operation – codenamed Neanderthals – are known to run the criminal enterprise as a
http://dlvr.it/SzJKh5
"Telekopye can craft phishing websites, emails, SMS messages, and more," ESET security researcher Radek Jizba said in a new analysis.
The threat actors behind the operation – codenamed Neanderthals – are known to run the criminal enterprise as a
http://dlvr.it/SzJKh5
Friday, November 24, 2023
Senior Ministers of State Visit Cyber Defence Exercise; Over 200 ... - MINDEF Singapore
Senior Ministers of State Visit Cyber Defence Exercise; Over 200 ... MINDEF Singapore
http://dlvr.it/SzGLxw
http://dlvr.it/SzGLxw
Saturday, November 11, 2023
Microsoft Warns of Fake Skills Assessment Portals Targeting IT Job Seekers
A sub-cluster within the infamous Lazarus Group has established new infrastructure that impersonates skills assessment portals as part of its social engineering campaigns.
Microsoft attributed the activity to a threat actor it calls Sapphire Sleet, describing it as a "shift in the persistent actor's tactics."
Sapphire Sleet, also called APT38, BlueNoroff, CageyChameleon, and CryptoCore, has a
http://dlvr.it/Syj76q
Microsoft attributed the activity to a threat actor it calls Sapphire Sleet, describing it as a "shift in the persistent actor's tactics."
Sapphire Sleet, also called APT38, BlueNoroff, CageyChameleon, and CryptoCore, has a
http://dlvr.it/Syj76q
“Cybersecurity Incident” Prompts Shutdown of DP World Australia ... - The Maritime Executive
“Cybersecurity Incident” Prompts Shutdown of DP World Australia ... The Maritime Executive
http://dlvr.it/Syhbs2
http://dlvr.it/Syhbs2
Friday, November 10, 2023
Cyber Security Today, Week in Review for the week ending Friday, Nov. 10, 2023 - IT World Canada
Cyber Security Today, Week in Review for the week ending Friday, Nov. 10, 2023 IT World Canada
http://dlvr.it/SyhLBP
http://dlvr.it/SyhLBP
SentinelOne to acquire cybersecurity consulting firm Krebs Stamos Group - The Record from Recorded Future News
SentinelOne to acquire cybersecurity consulting firm Krebs Stamos Group The Record from Recorded Future News
http://dlvr.it/Syg6Zm
http://dlvr.it/Syg6Zm
Russian Hackers Sandworm Cause Power Outage in Ukraine Amidst Missile Strikes
The notorious Russian hackers known as Sandworm targeted an electrical substation in Ukraine last year, causing a brief power outage in October 2022.
The findings come from Google's Mandiant, which described the hack as a "multi-event cyber attack" leveraging a novel technique for impacting industrial control systems (ICS).
"The actor first used OT-level living-off-the-land (LotL) techniques to
http://dlvr.it/Syfjjh
The findings come from Google's Mandiant, which described the hack as a "multi-event cyber attack" leveraging a novel technique for impacting industrial control systems (ICS).
"The actor first used OT-level living-off-the-land (LotL) techniques to
http://dlvr.it/Syfjjh
Tri-City Healthcare halts emergency operations after ransomware attack: source - NBC San Diego
Tri-City Healthcare halts emergency operations after ransomware attack: source NBC San Diego
http://dlvr.it/SyfKQZ
http://dlvr.it/SyfKQZ
Payments platform Fawry crashes but company denies cyber attack or data breaches - The National
Payments platform Fawry crashes but company denies cyber attack or data breaches The National
http://dlvr.it/SyfK17
http://dlvr.it/SyfK17
Thursday, November 9, 2023
New Malvertising Campaign Uses Fake Windows News Portal to Distribute Malicious Installers
A new malvertising campaign has been found to employ fake sites that masquerade as legitimate Windows news portal to propagate a malicious installer for a popular system profiling tool called CPU-Z.
"This incident is a part of a larger malvertising campaign that targets other utilities like Notepad++, Citrix, and VNC Viewer as seen in its infrastructure (domain names) and cloaking templates used
http://dlvr.it/Sydyrh
"This incident is a part of a larger malvertising campaign that targets other utilities like Notepad++, Citrix, and VNC Viewer as seen in its infrastructure (domain names) and cloaking templates used
http://dlvr.it/Sydyrh
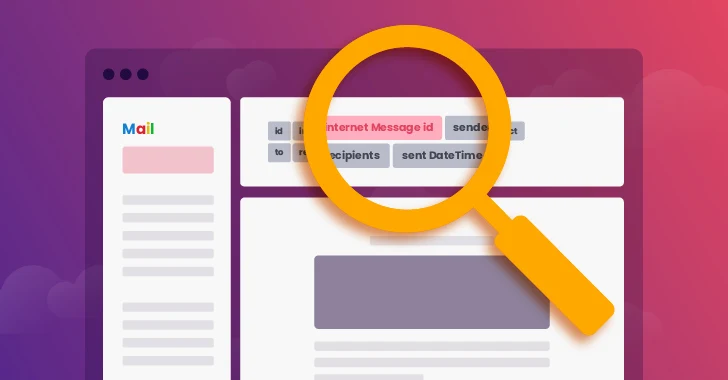
When Email Security Meets SaaS Security: Uncovering Risky Auto-Forwarding Rules
While intended for convenience and efficient communication, email auto-forwarding rules can inadvertently lead to the unauthorized dissemination of sensitive information to external entities, putting confidential data at risk of exposure to unauthorized parties. Wing Security (Wing), a SaaS security company, announced yesterday that their SaaS shadow IT discovery methods now include a solution
http://dlvr.it/Syc7PP
http://dlvr.it/Syc7PP
MuddyC2Go: New C2 Framework Iranian Hackers Using Against Israel
Iranian nation-state actors have been observed using a previously undocumented command-and-control (C2) framework called MuddyC2Go as part of attacks targeting Israel.
"The framework's web component is written in the Go programming language," Deep Instinct security researcher Simon Kenin said in a technical report published Wednesday.
The tool has been attributed to MuddyWater, an Iranian
http://dlvr.it/Syc70T
"The framework's web component is written in the Go programming language," Deep Instinct security researcher Simon Kenin said in a technical report published Wednesday.
The tool has been attributed to MuddyWater, an Iranian
http://dlvr.it/Syc70T
Bitsight continues strong investment in Europe, appoints security ... - PR Newswire
Bitsight continues strong investment in Europe, appoints security ... PR Newswire
http://dlvr.it/SybjkZ
http://dlvr.it/SybjkZ
Wednesday, November 8, 2023
Beware, Developers: BlazeStealer Malware Discovered in Python Packages on PyPI
A new set of malicious Python packages has slithered their way to the Python Package Index (PyPI) repository with the ultimate aim of stealing sensitive information from compromised developer systems.
The packages masquerade as seemingly innocuous obfuscation tools, but harbor a piece of malware called BlazeStealer, Checkmarx said in a report shared with The Hacker News.
"[BlazeStealer]
http://dlvr.it/SybLzj
The packages masquerade as seemingly innocuous obfuscation tools, but harbor a piece of malware called BlazeStealer, Checkmarx said in a report shared with The Hacker News.
"[BlazeStealer]
http://dlvr.it/SybLzj
Subscribe to:
Posts (Atom)
Cybersecurity needs AI as much as AI needs cybersecurity - Techzine Europe
Cybersecurity needs AI as much as AI needs cybersecurity Techzine Europe http://dlvr.it/TDY1dr